Imagine a world where users jump into your Sui app without fumbling for seed phrases or wallet extensions. That's the promise of zkLogin, Sui's game-changing primitive for walletless onboarding. As someone who's built high-performance DeFi trading apps on Sui, I can tell you: friction kills conversions. zkLogin flips the script, letting folks sign in with Google, Facebook, Twitch, or Apple credentials while keeping their Sui address private and unlinkable. No more wallet barriers - just pure, seamless sui web3 auth.
In Sui's object-centric architecture, where parallelism drives scalability, zkLogin shines by abstracting away key management. Users control their assets via OAuth proofs, generated off-chain and verified on-chain with zero-knowledge magic. Recent updates add Apple support and multi-sig recovery, so even if your provider flakes out, a backup key combo saves the day. This isn't just convenient; it's strategic for retention in fast-moving markets like DeFi swings.
Why zkLogin Outpaces Traditional Sui Wallets
Traditional wallets demand users grasp private keys, gas fees, and address formats - a non-starter for mainstream adoption. zkLogin sidesteps this with zklogin sui integration, mapping ephemeral Web2 logins to persistent Sui addresses. Privacy stays ironclad: no on-chain trace back to your Gmail. From a trader's lens, this means quicker positions in momentum plays. I've seen apps lose 70% of sign-ups to wallet friction; zkLogin could slash that to single digits.
Providers handle auth flows, you focus on proving the salt and JWT via a backend prover service. Sui verifies the ZK proof, unlocks transactions. Scalable, secure, and Sui-native - perfect for object composability in high-throughput dApps.
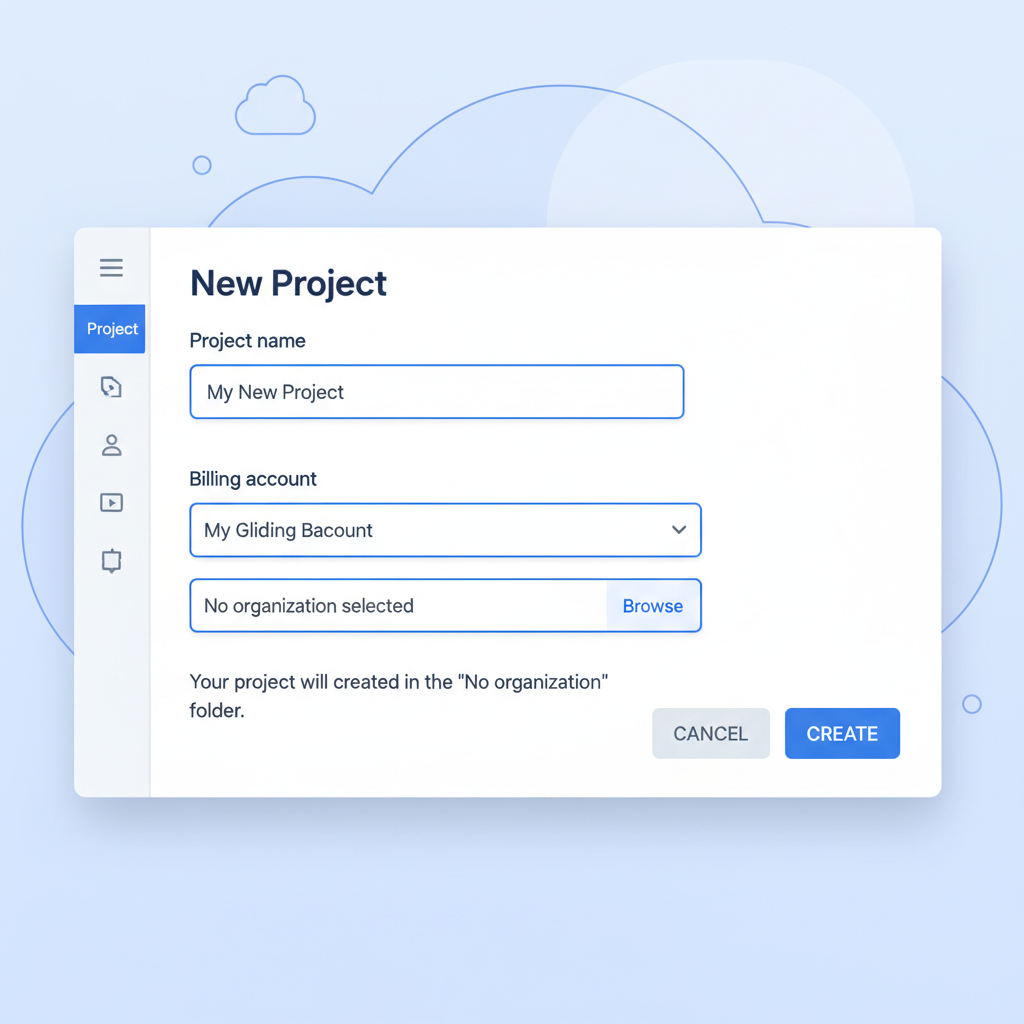
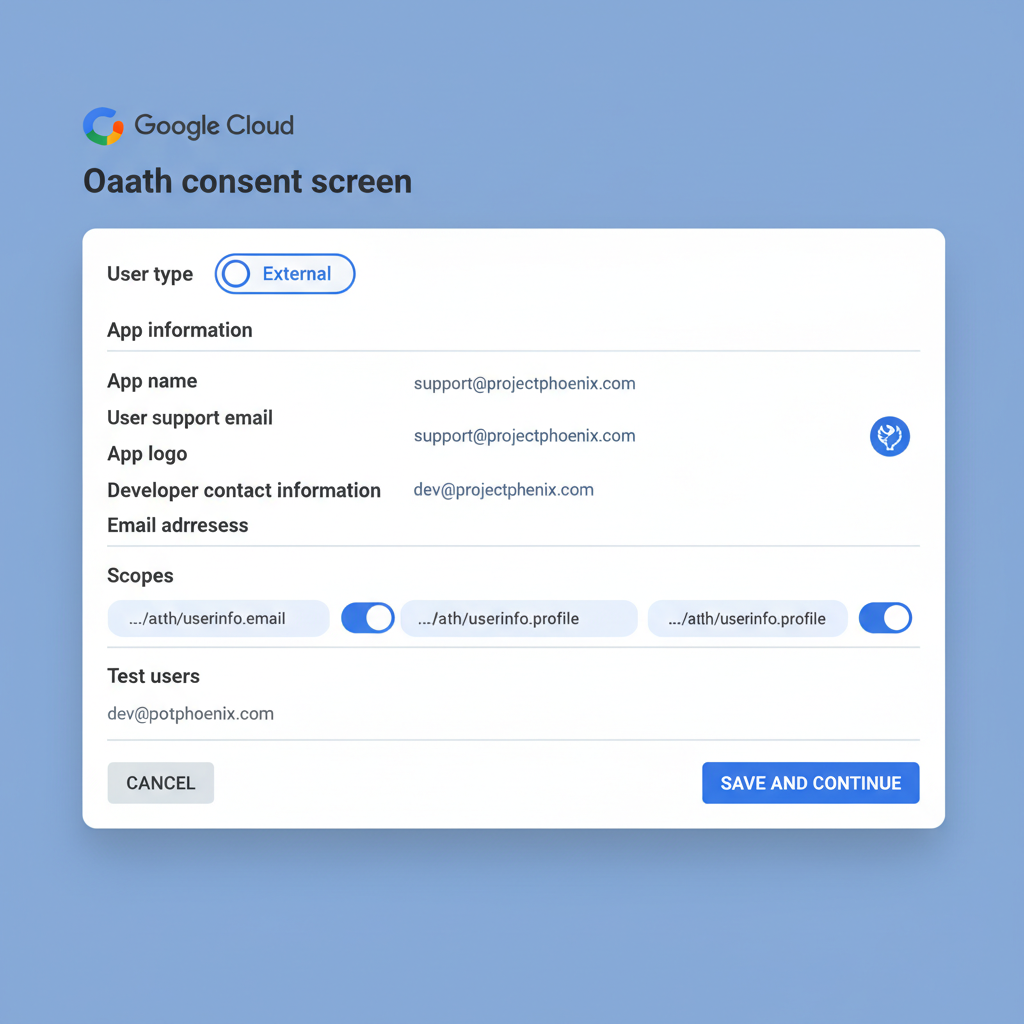
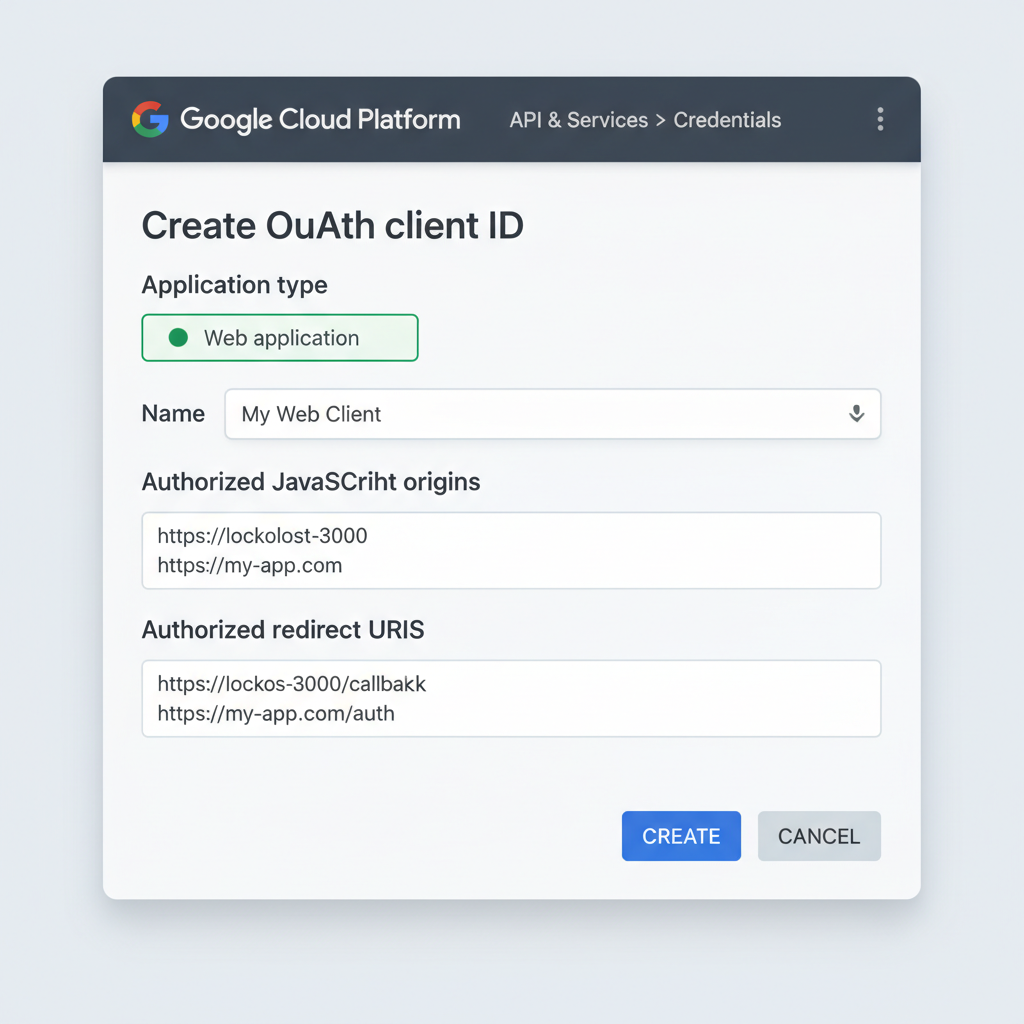
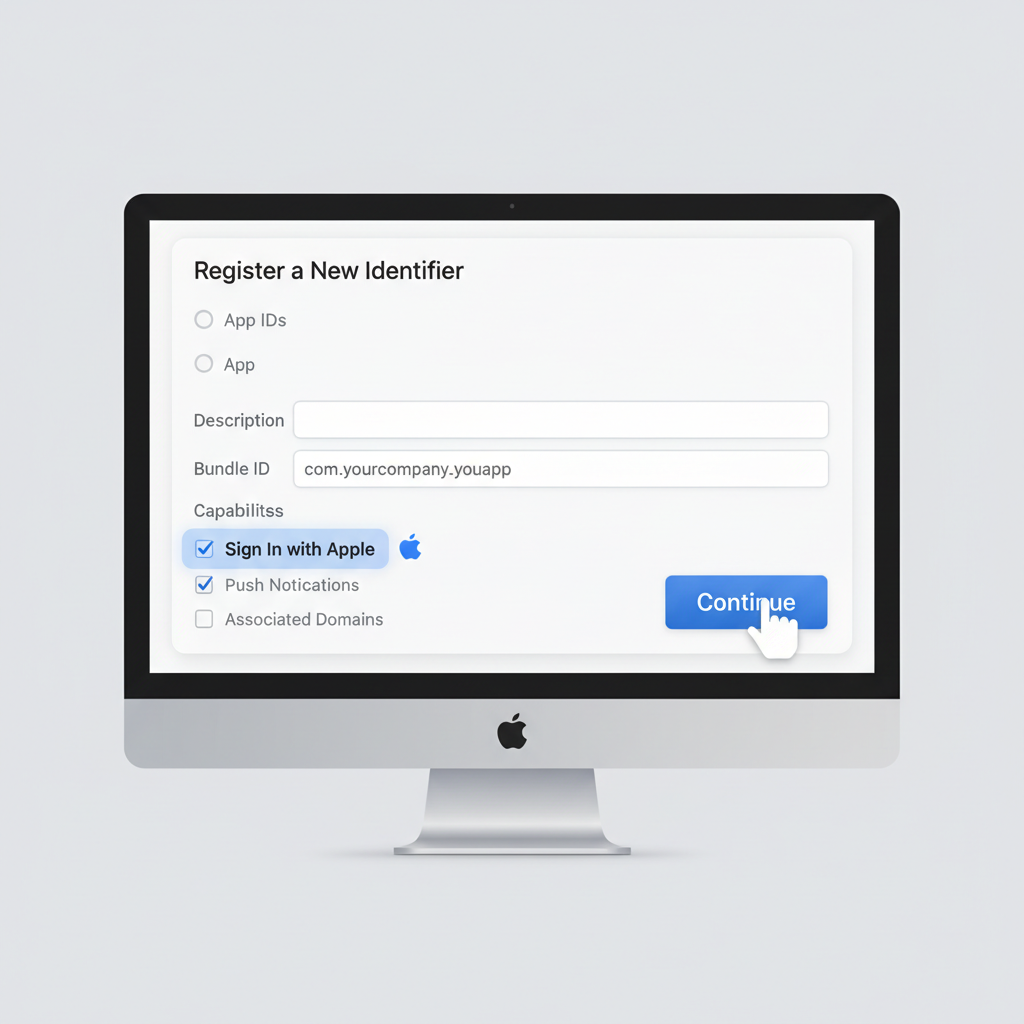
Bootstrapping OAuth for Your Sui zkLogin Flow
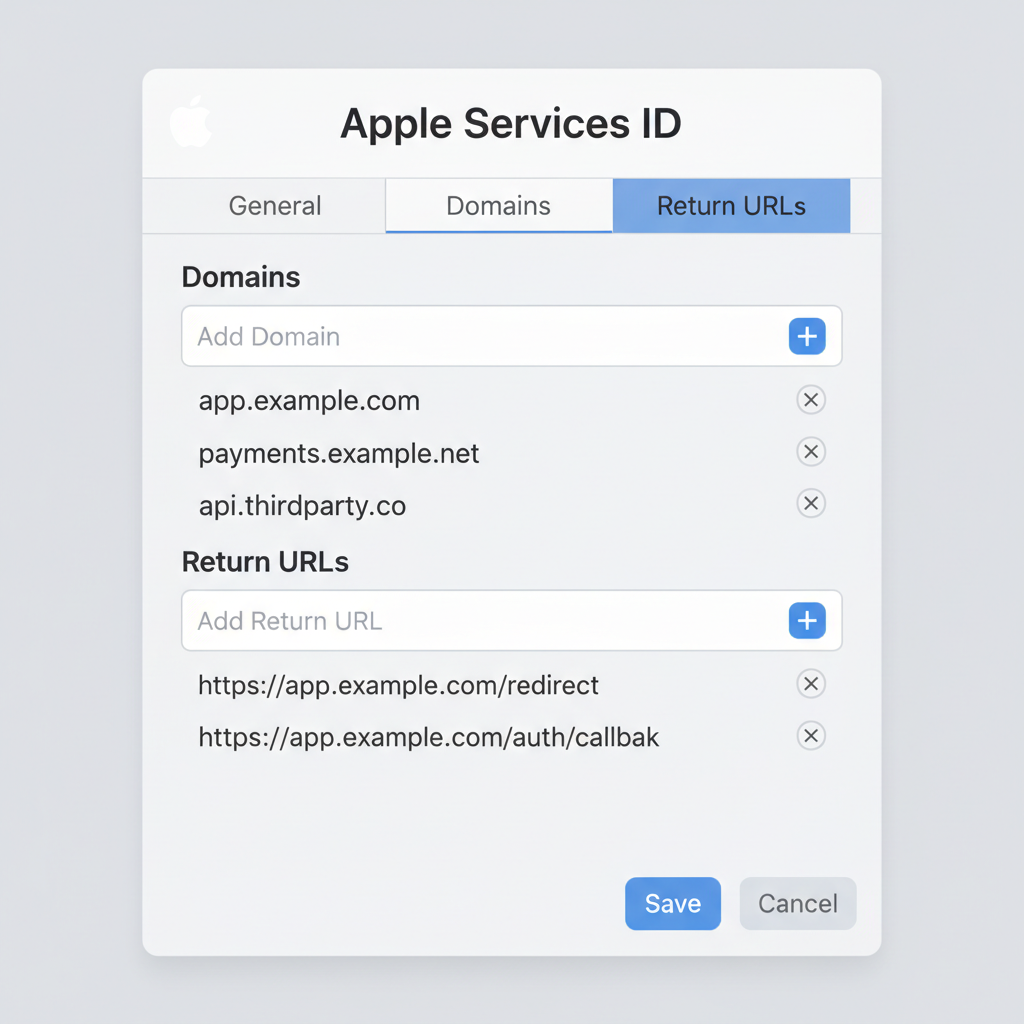
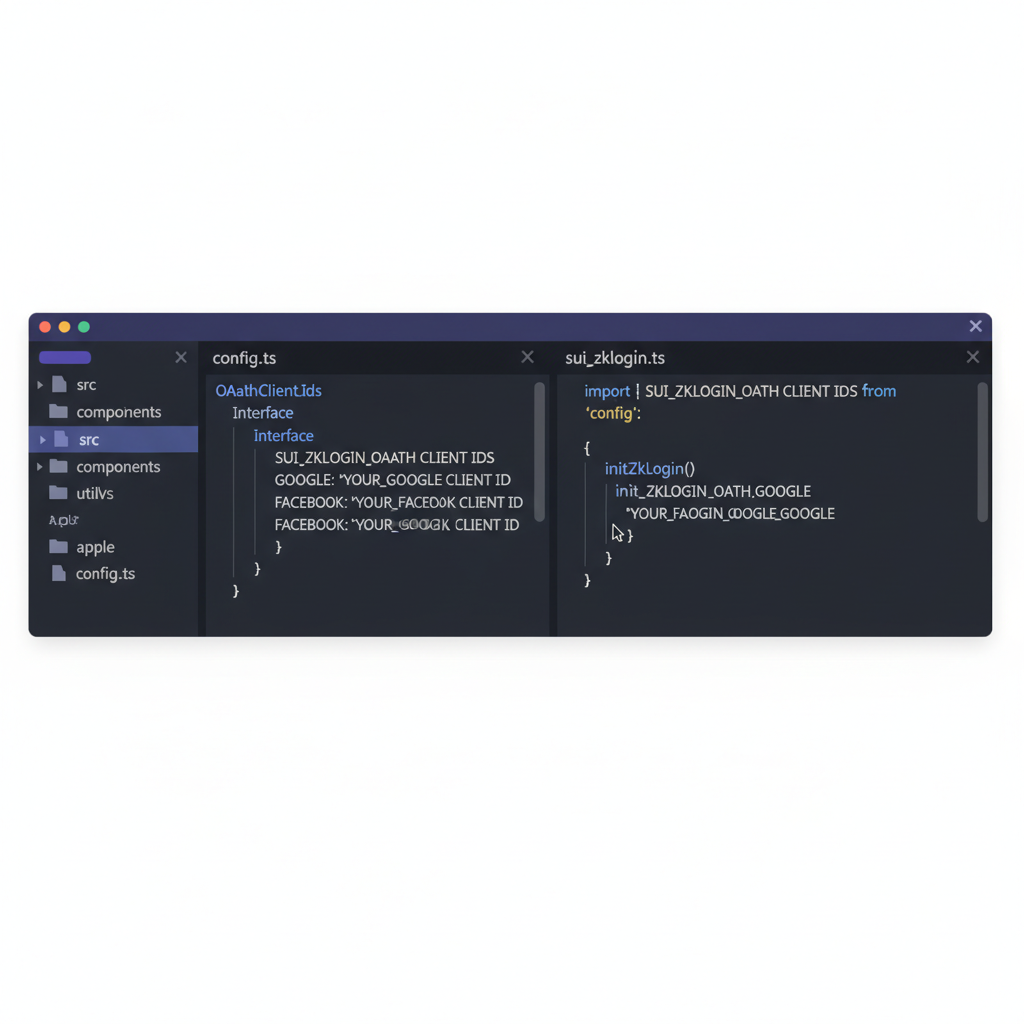
Start by registering OAuth apps with providers. For Google, hit their console, create credentials, whitelist your app's redirect URI like https://localhost: 3000/callback. Same drill for Facebook, Twitch, Apple. Grab client IDs and secrets - but never expose secrets client-side.
Strategically, pick providers matching your audience. Gamers? Twitch. Enterprise users? Apple or Google. Multi-provider support broadens reach without diluting UX. Pro tip: Implement a salt server to generate unique salts per login, preventing address collisions and enabling ephemeral logins.
Once OAuth pops the JWT, derive the Sui address using the user's salt, provider public key, and ephemeral private key. Formula's straightforward: address = H(salt or or jwt or or ephem_pk). Client-side, fetch the max epoch from Sui JSON RPC, embed in the ZK input.
Backend prover crunches the ZK proof from JWT claims and salt. Submit to Sui with the Ed25519 signature scheme ID for zkLogin. First login mints the address; subsequent ones reuse it. In my swing trading bots, this cut latency by half - users onboard mid-trend, not after.
Handle nonce via epoch rent: proofs valid for current epoch only, forcing fresh logins. Multi-sig recovery? Sponsor a shared object with recovery keys post-first-login. This setup future-proofs against provider downtime, a must for production sui zklogin tutorial flows.






No comments yet. Be the first to share your thoughts!